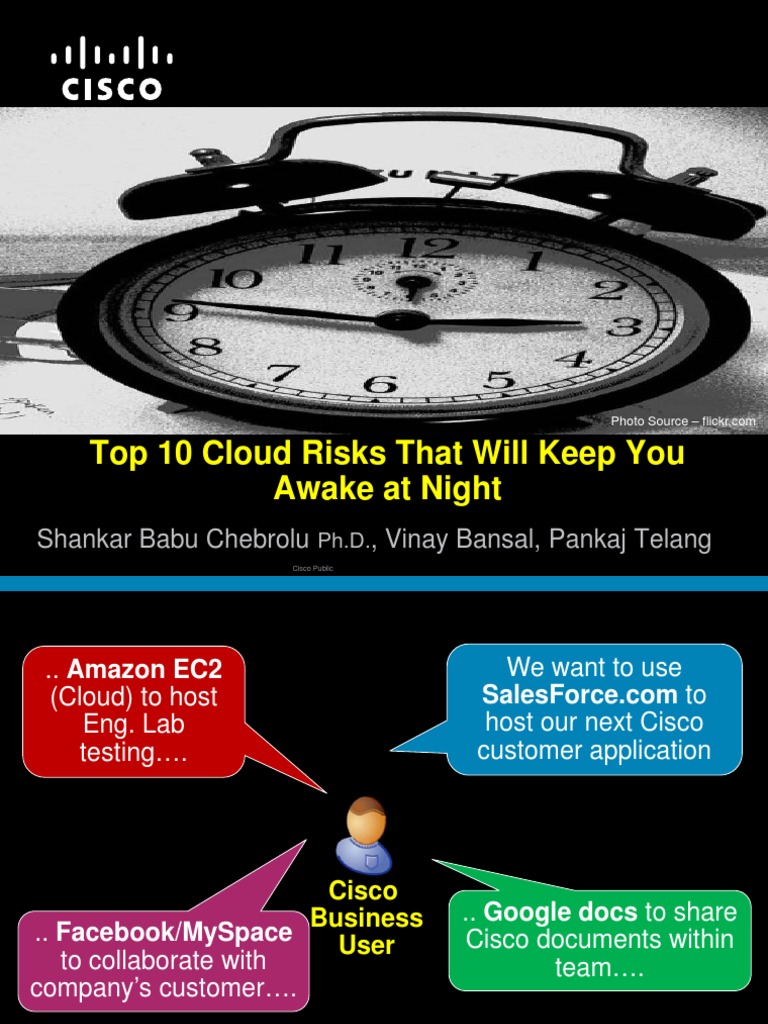
In today’s digital landscape, organizations increasingly rely on cloud computing solutions to foster operational agility and enhance collaboration. However, as enterprises migrate their data and applications to the cloud, they inadvertently expose themselves to a plethora of security risks. Understanding these vulnerabilities is crucial to safeguarding sensitive information and maintaining compliance with industry regulations. Below, we delve into the top 10 cloud security risks that organizations should not overlook.
1. Data Breaches
Data breaches remain a perennial threat within cloud environments, often leading to the unauthorized access of sensitive information. Cybercriminals exploit vulnerabilities in cloud configurations, mismanaged permissions, and insecure access protocols. A single breach can compromise customer data, intellectual property, and even lead to severe legal repercussions. Given the potential ramifications, organizations must implement robust encryption measures and access controls to mitigate this risk.
2. Insecure APIs
Application Programming Interfaces (APIs) are integral to the functionality of cloud services. However, they can become gateways for attacks if not adequately secured. Insecure APIs can lead to data leaks and service disruptions. To combat this, organizations need to utilize secure coding practices, conduct regular API security assessments, and employ strong authentication mechanisms to fortify these crucial interfaces.
3. Insufficient Identity and Access Management
With numerous users accessing cloud services, improper identity and access management opens the door to malicious activities. Weak passwords, lack of multi-factor authentication, and poorly configured user roles may allow unauthorized individuals to gain access to sensitive data. Robust identity and access management policies, coupled with regular audits, can significantly reduce this risk by ensuring that users have only the necessary permissions to perform their roles.
4. Malicious Insiders
Insider threats, whether from disgruntled employees or inadvertent mistakes, pose a significant risk to cloud security. Employees may unintentionally expose sensitive information or intentionally sabotage data. Conducting thorough background checks during the hiring process and fostering a strong corporate culture can help mitigate insider threats. Educating employees about phishing scams and other social engineering techniques is also paramount.
5. Lack of Compliance
Compliance is an ongoing challenge in the cloud, especially as regulatory frameworks evolve. Organizations must navigate an intricate landscape of laws and standards, such as GDPR and HIPAA. Non-compliance not only results in hefty fines but can tarnish an organization’s reputation. Establishing a compliance-focused culture and employing automated compliance tools can facilitate adherence to required regulations and mitigate risks.
6. Data Loss
Data loss can be caused by various factors, including accidental deletions, service outages, or malicious attacks. Organizations often assume that cloud service providers will back up their data, but this is not always the case. Without stringent data backup and recovery protocols, organizations risk irreversible data loss. Adopting a comprehensive data management strategy that includes regular backups and robust disaster recovery options is essential.
7. Vendor Lock-in
Vendor lock-in occurs when a company is dependent on a single cloud service provider, making it arduous and costly to change providers. This dependency may lead to security risks as organizations may hesitate to migrate due to the complexity involved. A diverse cloud strategy that employs a multi-cloud approach can alleviate this risk, enabling businesses to take advantage of various vendors’ strengths while safeguarding their data across platforms.
8. Unpatched Software Vulnerabilities
Cloud environments often rely on a mix of specialized software and operating systems. Failure to apply security patches promptly can leave these systems susceptible to exploitation. Cybercriminals frequently target known vulnerabilities in outdated software to infiltrate organizations. Maintaining an inventory of all software and instituting a regular patch management schedule will leave enterprises better fortified against emerging threats.
9. Inadequate Security Configurations
Misconfigurations of cloud environments are alarmingly common and can have dire consequences. Even minor oversights, such as leaving storage buckets exposed or disabling essential security features, can lead to significant security breaches. Adopting a security-first mindset during the cloud setup process, conducting regular configuration audits, and leveraging automation tools can assist organizations in detecting misconfigurations before they are exploited.
10. Limited Visibility and Control
Cloud infrastructures typically lack the same visibility and control as on-premises systems, complicating risk management efforts. Organizations may struggle to monitor activities and effectively analyze potential threats in real time. Implementing comprehensive security information and event management (SIEM) solutions can enhance visibility across cloud environments, allowing organizations to proactively detect and respond to security incidents.
In conclusion, while cloud computing offers unparalleled advantages, it also presents a myriad of security risks that organizations must confront head-on. By recognizing and addressing these vulnerabilities, businesses can not only protect their data but also strengthen their overall cybersecurity posture. Being aware of these risks and investing in proper security measures will cultivate trust among customers and stakeholders alike, ensuring a resilient and secure cloud strategy for the future.










Leave a Comment