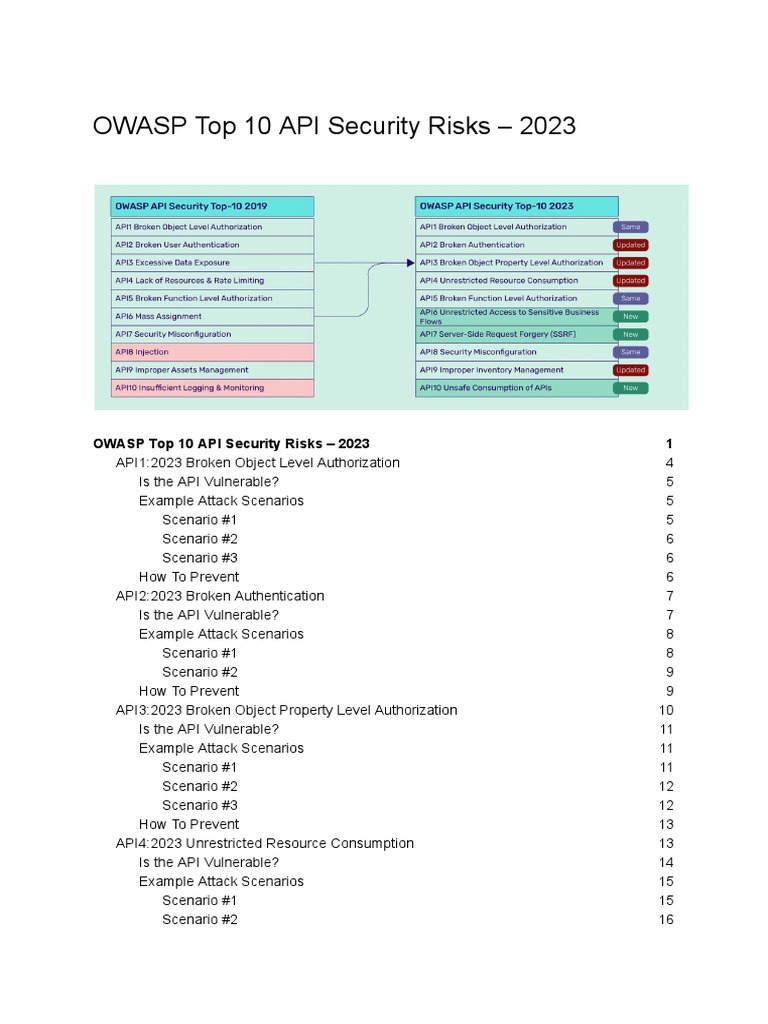
In the rapidly evolving landscape of digital technology, Application Programming Interfaces (APIs) serve as the backbone of modern applications. They enable disparate systems to communicate seamlessly and foster an ecosystem of creativity and innovation. However, with the increasing reliance on APIs comes a corresponding uptick in security threats, prompting the Open Web Application Security Project (OWASP) to offer its latest insights. The OWASP API Security Top 10 for the years 2023 to 2025 highlights a critical evaluation of risks that developers and organizations must navigate in order to safeguard their digital assets. Herein lies an exploration of these emerging threats that capture the attention of security professionals and technologists alike.
1. Broken Object Level Authorization
One of the most pervasive threats in API security is broken object-level authorization. This vulnerability allows attackers to manipulate API requests and gain unauthorized access to data they shouldn’t see. It’s akin to finding an unlocked cabinet filled with sensitive files—no sophisticated hacking required. The need for robust authorization checks becomes paramount, illustrating a gap where organizations often fall short in security protocols.
2. Excessive Data Exposure
APIs often return more information than necessary in response to a query, which can lead to excessive data exposure. This phenomenon can result from poor design decisions, such as failing to enforce proper filtering. Organizations must scrutinize their API responses to ensure they only divulge essential information. Unguarded endpoints can unwittingly reveal a treasure trove of sensitive data, inviting exploitation.
3. Lack of Resource and Rate Limiting
As APIs handle increasing volumes of requests, the lack of proper resource and rate limiting can lead to denial of service and resource exhaustion. Unscrupulous users can overwhelm services with an avalanche of requests, leading to detrimental downtime. Developers must implement strict thresholds and monitoring to protect against this type of abuse, preserving user experience and service availability.
4. Broken Function Level Authorization
In the world of APIs, broken function-level authorization presents a unique challenge. Uneven access privileges can allow users to invoke a function meant for a different class of users, compromising data security. This vulnerability calls for meticulous role-based access controls, ensuring that only authorized personnel can engage specific API functionalities, thus maintaining the sanctity of sensitive operations.
5. Mass Assignment
Mass assignment vulnerabilities stem from APIs that naively trust information from client-side inputs. Attackers exploit this by sending unexpected data fields, affecting properties beyond the intended scope. This risk underscores the importance of strict validation and limiting data fields to those necessary for operations, enforcing a more disciplined approach to data handling.
6. Security Misconfiguration
Security misconfiguration is often the result of insufficiently hardened APIs. Often, default configurations are left unchanged, creating opportunities for exploitation. Regular audits and adherence to best practices can mitigate this risk. It requires continuous vigilance to fortify security posture, especially as cloud-based resources and services proliferate.
7. Injection Flaws
Injection flaws, especially those pertaining to APIs, remain a critical threat vector. Whether it’s through SQL, NoSQL, or Command Injection, insufficient input sanitization can lead to catastrophic security breaches. API developers must implement rigorous validation measures and employ parameterized queries as best practices to thwart such attacks, ensuring the integrity of their systems.
8. Improper Assets Management
The proliferation of APIs can lead to a lack of visibility and cataloging of accessible endpoints. As development teams grow and projects scale, it becomes easier for obsolete or vulnerable APIs to linger without oversight. Organizations must practice diligent asset management, ensuring that all APIs in use are accounted for and appropriately secured, including the decommissioning of outdated APIs that may pose security risks.
9. Insufficient Logging and Monitoring
In an age where effective incident response is paramount, insufficient logging and monitoring can hinder an organization’s ability to detect and respond to breaches. The absence of comprehensive logs leaves dark alleys where malevolent actors operate undetected. Effective logging is not merely a compliance measure; it is a vital component of any security strategy, allowing for timely identification and response to security incidents.
10. Insecure API Lifecycle Management
The insecure management of an API’s lifecycle, from design to deployment and decommissioning, can expose vulnerabilities at every stage. Inconsistent application of security practices across an API’s lifecycle can leave chinks in the armor. Organizations must embed security controls from the outset, treating security as a fundamental aspect rather than an afterthought, ensuring a more robust API posture throughout its existence.
As organizations forge ahead into the next few years, the OWASP API Security Top 10 serves as an invaluable compass in the perilous waters of API security. The threats outlined are not merely technical deficiencies; they represent profound insights into the architectural challenges and complacencies ingrained in modern development practices. Effective mitigation strategies demand not just awareness of these vulnerabilities but also a cultural shift towards rigorous security advocacy and the integration of best practices in every facet of the API lifecycle. As development teams tread this intricate landscape, a proactive approach to these threats will differentiate successful, secure applications from those doomed to insecurity.







Leave a Comment