The digital landscape is a multifaceted realm where security is paramount. As software continues to evolve, so too do the vulnerabilities that threaten it. This evolution is captured succinctly in the OWASP Top 10, a pivotal list that highlights the most critical security risks faced by web applications. With the impending release of the OWASP Top 10 for 2025, a fresh perspective emerges, inviting technologists, developers, and organizations to recalibrate their security paradigms. Here, we delve into the anticipated risks revealed in the latest iteration, unveiling the implications each holds for stakeholders in the cyber realm.
1. Insecure Deserialization
Insecure deserialization takes center stage as organizations grapple with the devastating impact of manipulated serialized objects. Cybercriminals exploit this vulnerability by injecting malicious payloads into serialized data, leading to remote code execution and an array of subsequent attacks. Detailed insights into how deserialization works alongside best practices for secure implementations become crucial for organizations aiming to fortify application integrity.
2. API Misconfiguration
Application Programming Interfaces (APIs) serve as conduits for modern software, yet they remain vulnerable to misconfiguration. As businesses increasingly rely on third-party APIs, neglecting to secure these gateways leaves them exposed to unwanted breaches. From over-permissive access controls to insecure endpoints, the myriad factors contributing to API vulnerabilities underscore the necessity of stringent API security practices. Regular audits and security protocols are vital to ensure that these vectors remain watertight.
3. Insufficient Logging & Monitoring
Insufficient logging and monitoring weave a painful narrative where breaches go unnoticed until substantial damage has occurred. Without an intricate logging mechanism, organizations can neither detect anomalies nor respond promptly to incidents. The sophistication of today’s attacks necessitates a robust monitoring framework that not only records events but also analyzes them for potential threats. A proactive stance on logging enhances the ability to trace activities and learn from past vulnerabilities.
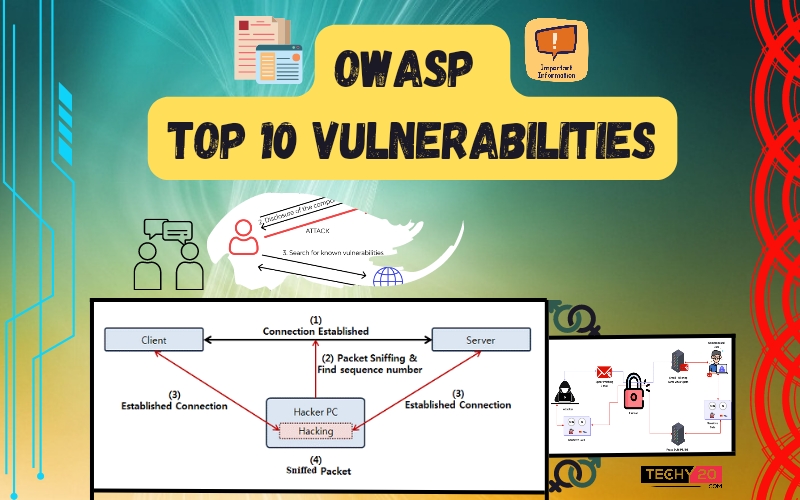
4. Component Vulnerabilities
With software development requiring a multitude of components, ranging from libraries to frameworks, vulnerabilities within these elements can jeopardize entire applications. Component vulnerabilities exemplify the importance of maintaining an up-to-date inventory and routinely scanning for known vulnerabilities. Strengthening dependencies through diligent patch management not only mitigates risk but fosters a culture of continuous improvement in security hygiene.
5. Cross-Site Scripting (XSS) Evolutions
Cross-Site Scripting, often categorized as a classic vulnerability, adapts as attackers refine their techniques. Modern XSS attacks can now bypass traditional defenses, rendering applications susceptible to session hijacking and theft of sensitive information. It is imperative for developers to adopt rigorous input validation and implement Content Security Policies (CSP) as defenses. Recognizing the nuanced methods employed in contemporary XSS exploits prepares organizations to withstand such onslaughts.
6. Credential Stuffing & Account Takeover
As users juggle an increasing number of credentials across platforms, the vulnerability of credential stuffing gains prominence. Attackers utilize stolen credentials from breaches to automate login attempts across different sites, leading to unauthorized account access. This invites a reevaluation of authentication mechanisms. Employing multi-factor authentication (MFA) and fostering a habit of routinely changing passwords can significantly bolster defenses against account takeovers.
7. Insecure Direct Object References (IDOR)
IDOR represents a pervasive misstep in access control implementations, allowing attackers to manipulate URLs or form parameters to access unauthorized data. As data protection regulations tighten, the implications of IDOR extend beyond mere security issues; they encompass legal ramifications as well. Constructing a robust access control layer and leveraging security measures like object ID validation can help protect sensitive resources from unauthorized access.
8. Supply Chain Attacks
The interconnected web of software dependencies makes supply chain attacks alarmingly feasible. By compromising a single component within an organization’s supply chain, perpetrators can infiltrate entire ecosystems. The focus on supply chain security necessitates a paradigm shift; organizations must prioritize the security of not only their own applications but also that of their vendors. Employing rigorous vetting processes and security assessments of third-party software suppliers becomes paramount in mitigating these risks.
9. Threats from Automation & AI
With the rise in automation and the increasing reliance on artificial intelligence, the landscape of cyber threats morphs continuously. While these technologies offer immense benefits, they also present opportunities for adversaries to exploit. Attack simulations that leverage AI can evolve at an unprecedented pace. Therefore, organizations must cultivate a dual strategy that embraces automation for defensive purposes while remaining agile against automated threats. Education around AI vulnerabilities is crucial for an informed response.
10. Shadow IT and Data Leaks
The burgeoning trend of shadow IT—a manifestation of employees leveraging unsanctioned tools and applications—fuels the risk of data leaks. This behavior, while often well-intentioned, sidesteps organizational security protocols, leading to unmonitored data storage and potential breaches. Establishing a clear policy regarding acceptable use of technology and providing secure, sanctioned alternatives can rein in shadow IT practices. Implementing data loss prevention (DLP) measures further bolsters the security of sensitive information.
In summary, as the digital world evolves, so too must our approach to security. The OWASP Top 10 for 2025 not only sheds light on contemporary vulnerabilities but also urges all stakeholders to embrace a proactive, multifaceted strategy in safeguarding their assets. By delving into each risk with diligence and foresight, organizations can begin to reshape the future, mitigating threats before they escalate into crises.








Leave a Comment