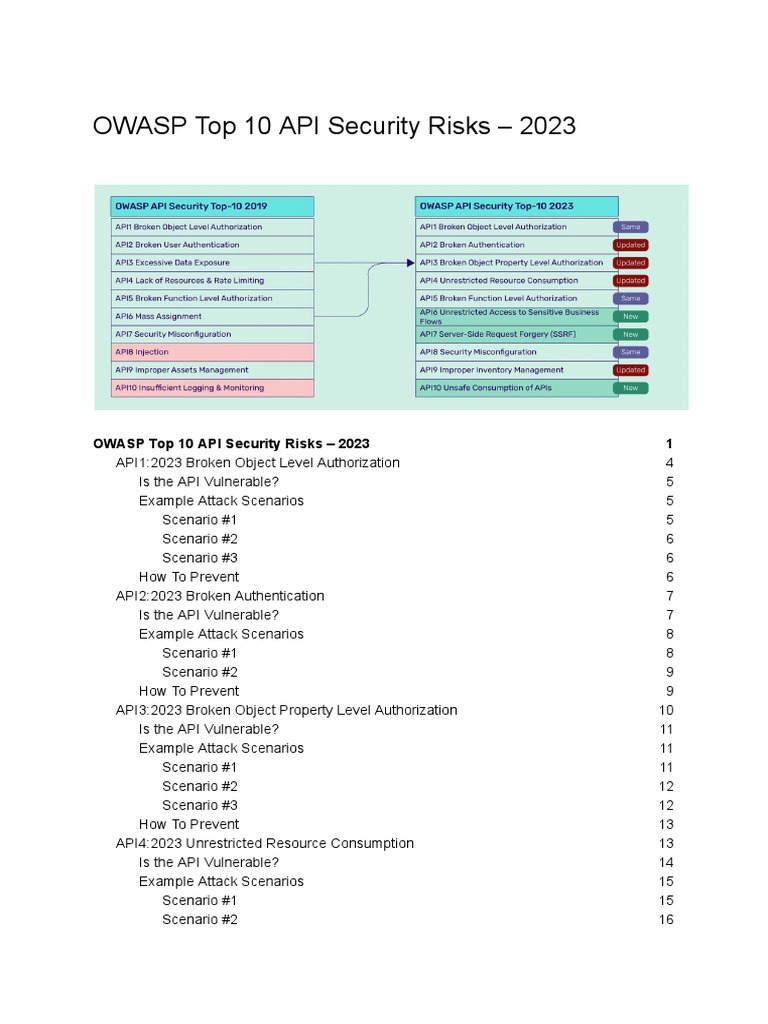
API security has become a significant focus for developers, businesses, and cybersecurity professionals alike. As organizations increasingly rely on APIs to facilitate data exchange and drive application functionality, the risks associated with their vulnerabilities have grown. The OWASP API Security Top 10 (2023) identifies the most critical threats that could jeopardize sensitive information and disrupt services. Understanding these risks not only highlights common vulnerabilities but also reveals deeper reasons why APIs remain a persistent target for attackers. This listicle delves into each of these top risks, providing clear and informative insights.
1. Broken Object Level Authorization
One of the most prevalent vulnerabilities involves improper enforcement of authorization checks for objects such as database records. Attackers can manipulate object IDs to access data or perform actions they shouldn’t be allowed to. This flaw exposes sensitive data and can lead to unauthorized operations inside the system.
2. Broken User Authentication
Authentication mechanisms that are insufficient or flawed allow attackers to compromise accounts or impersonate users. This risk may stem from weak password policies, session management issues, or reliance on insecure authentication flows, making APIs susceptible to unauthorized access.
3. Excessive Data Exposure
APIs sometimes return more data than necessary, trusting clients to filter out sensitive information. This reliance on client-side data filtering can expose confidential data unintentionally. Attackers who exploit this weakness can gain insights into backend structures or user details.
4. Lack of Resources & Rate Limiting
APIs that do not enforce limits on resource usage are vulnerable to denial-of-service (DoS) attacks or brute-force attempts. Inadequate throttling allows attackers to overwhelm the system or repeatedly try credentials, increasing risk and impacting service availability.
5. Broken Function Level Authorization
Unlike object-level authorization, this vulnerability pertains to inadequate verification of user privileges for specific functions or endpoints. Attackers can exploit this to perform restricted operations if the API fails to check permissions at the function level.
6. Mass Assignment
When APIs accept and bind client input to internal models without strict controls, attackers can manipulate properties they shouldn’t have access to, such as administrative flags or user roles. This can lead to privilege escalation or unauthorized data modification.
7. Security Misconfiguration
Failing to properly configure security settings within the API infrastructure opens doors for attacks. This includes default configurations, unnecessary HTTP methods enabled, or verbose error messages disclosing system information which accelerates attack reconnaissance.
8. Injection
Injection flaws occur when untrusted data is sent to an interpreter as part of a command or query. Common examples include SQL, NoSQL, and LDAP injection. Attackers can execute arbitrary commands, extract data, or manipulate backend systems if this risk is not addressed.
9. Improper Assets Management
APIs often have numerous endpoints, some deprecated or undocumented. Without proper lifecycle management and visibility, these forgotten endpoints may contain unpatched vulnerabilities or expose outdated functionality susceptible to exploitation.
10. Insufficient Logging & Monitoring
Without detailed logging and continuous monitoring, suspicious activities can go unnoticed. This deficiency delays detection and response to attacks, increasing potential damage. Effective logging also aids in incident investigation and compliance requirements.
11. Weak Cryptography
While encryption is vital, using outdated or weak cryptographic algorithms undermines data protection efforts. Attackers can exploit these weaknesses to intercept or tamper with sensitive information transmitted through APIs.
12. Insecure Direct Object References (IDOR)
This specific case of authorization failure involves manipulation of reference identifiers to access data belonging to other users. IDOR vulnerabilities are common and often result from insufficient access control on objects within APIs.
13. Insufficient Transport Layer Protection
Data transmitted without strong transport security (e.g., TLS) is vulnerable to interception and man-in-the-middle attacks. Ensuring TLS and enforcing secure communication protects the integrity and confidentiality of data traversing between clients and APIs.
14. Client-Side Security Issues
Many API clients can store tokens or sensitive data improperly, exposing them to theft or misuse. While server-side security is crucial, understanding the client environment is also essential to reduce attack surfaces related to API consumption.
15. Business Logic Vulnerabilities
Sometimes APIs succumb to flaws rooted in the application’s logic rather than technical bugs. Attackers manipulate workflow, abuse sequence of operations, or exploit logic assumptions to gain unintended advantages or bypass security measures.
16. Cross-Site Request Forgery (CSRF)
Though traditionally a web concern, APIs can be susceptible to CSRF attacks when relying on cookies for authentication. Attackers trick authenticated users into submitting unwanted requests, executing actions they did not intend.
17. Insufficient Input Validation
Failure to validate user-supplied input rigorously allows API consumers to send malformed or malicious data. This can result in crashes, code injections, or corrupted data processing within backend services.
18. Endpoint Enumeration
Through error messages or predictable API patterns, attackers can map the surface area of API endpoints. This reconnaissance assists in planning further attacks by identifying poorly secured or interesting functions to target.
The fascination with APIs among attackers stems from their integral role in modern applications, handling sensitive data and core business logic. Each risk in the OWASP API Security Top 10 shines a light on how easily these gateways can be exploited if not carefully secured. For organizations, addressing these vulnerabilities is essential not just for compliance, but to safeguard reputation and maintain trust in an increasingly connected digital landscape.








Leave a Comment